最牛B的Linux Shell命令 引言 Shell作为Unix系操作系统当中最有魅力且不可或缺的组件,经过数十载的洗礼不仅没有被淘汰,而且愈加变得成熟稳健,究其原因,大概因为它是个非常稳固的粘合剂,能够把大量功能强大的组件任意配搭,总能很好很快地完成用户的任务。
本文的一些命令很可能看起来是“雕虫小技”,我们只好仰慕一下Shell大牛了,但是有些细节我会稍加发掘加以说明,遇到有趣的地方希望能博您一笑了。
1.以sudo运行上条命令
大家应该都知sudo,不解释。但通常出现的情况是,敲完命令执行后报错才发现忘了sudo。这时候,新手用户就会:按上箭头,按左箭头,盯着光标回到开始处,输入sudo,回车;高手用户就蛋定多了,按Ctrl-p,按Ctrl-a,输入sudo,回车。
这里介绍这个是天外飞仙级别的,对,就直接sudo !!。
当然这几种解决方式效果是完全一样的,只是款不一样,嗯,不解释。
两个感叹号其实是bash的一个特性,称为事件引用符(event designators)。!!其实相当于!-1,引用前一条命令,当然也可以!-2,!-50。默认情况下bash会在~/.bash_history文件内记录用户执行的最近500条命令,history命令可以显示这些命令。
关于事件引用符的更多用法可以深入阅读The Definitive Guide to Bash Command Line History 。
2.以HTTP方式共享当前文件夹的文件
1
$ python -m SimpleHTTPServer 8080
这命令启动了Python的SimpleHTTPServer模块,考虑到Python在绝大多数的Linux发行版当中都默认安装,所以这个命令很可能是最简单的跨平台传文件的方法。
命令执行后将在本机8000端口开放HTTP服务,在其他能访问本机的机器的浏览器打开ttp://ip:8000即打开一个目录列表,点击即可下载。
python3的话
1 python3 -m http.server 8080
find 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 #最近一天修改的md文档 find . -maxdepth 1 -type f -mtime -1 -name "*.md" -not -name "template.md" -not -name "temp.md" -exec ls -lh "{}" \; find . -size 0 -type f -exec ls -lh "{}" \; find . -maxdepth 1 -type f -mtime -2 -name "*margin*" -exec mv "{}" /tmp/img/ \; #clean the big file, but exclude spill dir sudo find /home/admin/ -not -path "*/spill/*" -type f -size +3G -exec cp /dev/null {} \; sudo find /home/admin/ -type f -name "*.hprof" -mtime +1 -exec rm -f {} \; #clean the spill temp file which before 7 days ago sudo find /home/admin/ -type f -mtime +7 -exec cp /dev/null {} \; sudo find /home/admin/logs/ -type f -mtime +7 -exec rm -f {} \; sudo find /var/log/ -type f -size +500M -exec cp /dev/null {} \; // -mindepth 1 可以忽略当前目录的"." find . -mindepth 1 -maxdepth 1 -type d -mtime -50 #备份匹配的文件 find . -name '*.ibd' | grep tpcc1000 | grep -v mysql_global | xargs -I{} cp --path {} /tmp/bak/ #将yaml 备份,保留目录结构 find . -name '*.yaml' | xargs -I{} cp --path {} /tmp/ find $srcDir -maxdepth 1 -type f -mtime -$1 -name "*.md" -not -name "template.md" -not -name "temp.md" -exec ls -lh "{}" \; find $srcDir -maxdepth 1 -type f -mtime -$1 -name "*.md" -not -name "template.md" -not -name "temp.md" -exec cp "{}" ./source/_posts/ \; #sudo find /media/sf_D_DRIVE/case/ -maxdepth 1 -type f -mtime -$1 -name "*.md" -not -name "template.md" -print -exec cp "{}" ./source/_posts/ \; cat的时候输出文件名: find . -type f -print -exec cat {} \;
xargs 参数:
-I [replace-str]:将xargs的输出每一项参数,单独赋值给后面的命令,参数需要用指定的代替字符串replace-str代替,也就是说replace-str不可缺省,必须显示指明,可以使用{} $ @等符号,其主要作用是当xargs command后有多个参数时,调整参数位置
top 默认配置文件:/.toprc (on Ubuntu, it is */.config/procps/toprc*)
增加列:f (此时可以调整用 → 选择列并调整位置, 此时也有4个窗口可以选择)
按node展示cpu:2(3 选择需要展示的node)
按core展示cpu: 1
切换颜色:z (有4个窗口可以选择,按 g 可以选择1-4)
配置颜色: Z
V 切换成森林视图,也就是展示进程父子关系
保存配置: W
1 dG9wJ3MgQ29uZmlnIEZpbGUgKExpbnV4IHByb2Nlc3NlcyB3aXRoIHdpbmRvd3MpCklkOmksIE1vZGVfYWx0c2NyPTAsIE1vZGVfaXJpeHBzPTEsIERlbGF5X3RpbWU9My4wLCBDdXJ3aW49MApDcHUJZmllbGRzY3VyPaWmqLWztLu9wMS3urg5xScpKissLS4vMDEyNjw+P0FCQ0ZHSElKS0xNTk9QUVJTVFVWV1hZWltcXV5fYGFiY2RlZmdoaWoKCXdpbmZsYWdzPTE5NTM4MCwgc29ydGluZHg9MTgsIG1heHRhc2tzPTAsIGdyYXBoX2NwdXM9MCwgZ3JhcGhfbWVtcz0wCglzdW1tY2xyPTQsIG1zZ3NjbHI9MSwgaGVhZGNscj0zLCB0YXNrY2xyPTQKTWVtCWZpZWxkc2N1cj2lu73AvMPBws3OJjk3uigzNEQnxSkqKywtLi8wMTI1Njg+P0ZHSElKS0xPUFFSU1RVVldYWVpbXF1eX2BhYmNkZWZnaGlqCgl3aW5mbGFncz0xOTUzODAsIHNvcnRpbmR4PTIxLCBtYXh0YXNrcz0wLCBncmFwaF9jcHVzPTAsIGdyYXBoX21lbXM9MAoJc3VtbWNscj02LCBtc2dzY2xyPTYsIGhlYWRjbHI9MywgdGFza2Nscj02ClNjaAlmaWVsZHNjdXI9pTo7PD0+P0BBTUJOQ7WztMfEtre5xcYmJygpKissLS4vMDEyOEhJSktMT1BRUlNUVVZXWFlaW1xdXl9gYWJjZGVmZ2hpagoJd2luZmxhZ3M9MTk0ODY4LCBzb3J0aW5keD0wLCBtYXh0YXNrcz0wLCBncmFwaF9jcHVzPTAsIGdyYXBoX21lbXM9MAoJc3VtbWNscj01LCBtc2dzY2xyPTUsIGhlYWRjbHI9MywgdGFza2Nscj01CkNncAlmaWVsZHNjdXI9paanqCowOTc6RCkrLC0uLzEyMzQ1Njg7PD0+P0BBQkNGR8hJSktMTU5P0NHS09TVxVZXWFlaW1xdXl9gYWJjZGVmZ2hpagoJd2luZmxhZ3M9MTk0ODY4LCBzb3J0aW5keD0wLCBtYXh0YXNrcz0wLCBncmFwaF9jcHVzPTAsIGdyYXBoX21lbXM9MAoJc3VtbWNscj0yLCBtc2dzY2xyPTMsIGhlYWRjbHI9MywgdGFza2Nscj0yCkZpeGVkX3dpZGVzdD0wLCBTdW1tX21zY2FsZT0wLCBUYXNrX21zY2FsZT0wLCBaZXJvX3N1cHByZXNzPTAKCnBpcGUJTmV0RmlsZXMJbHNvZiAtYSAtbCAtbiAtUCAtaTQgLXAgJWQgMj4mMQpwaXBlCU9wZW5GaWxlcwlsc29mIC1hIC1sIC1uIC1QIC1wICVkIDI+JjEKZmlsZQlOVU1BSW5mbwkvcHJvYy8lZC9udW1hX21hcHMK
xargs 传参数
ls /xx | xargs -t -I{} cp {} /tmp/{}
-t : 打印内容,去掉\n之后的字符串
-I : 后面定义占位符,上例子是{} ,后面命令行中可以多次使用占位符
挂载多台苹果的例子
idevice_id -l|xargs -t -I{} mkdir {};idevice_id -l |xargs -t -I{} ifuse {} {}
批量执行docker exec
1 ansible -i host.ini all -m shell -a "docker ps -a | grep tpcc | grep dn | cut -d ' ' -f 1 | xargs -I{} docker exec {} bash -c \"myc -e 'shutdown'\""
批量推送镜像
1 docker images |grep "docker.io:5000" | awk '{ print $1":"$2 }' | xargs -I {} docker push {}
非贪婪匹配 vim中默认匹配:abc.*d 是贪婪匹配,也就是尽可能长地匹配,改用 abc.{-}d 匹配到第一个 d字符就结束
贪婪模式是: .*
非贪婪模式是: .\{-}
1 2 3 4 5 6 7 8 9 10 11 \{n,m} Matches n to m of the preceding atom, as many as possible \{n} Matches n of the preceding atom \{n,} Matches at least n of the preceding atom, as many as possible \{,m} Matches 0 to m of the preceding atom, as many as possible \{} Matches 0 or more of the preceding atom, as many as possible (like *) */\{-* \{-n,m} matches n to m of the preceding atom, as few as possible \{-n} matches n of the preceding atom \{-n,} matches at least n of the preceding atom, as few as possible \{-,m} matches 0 to m of the preceding atom, as few as possible \{-} matches 0 or more of the preceding atom, as few as possibles
grep 非贪婪匹配
1 2 3 grep --color -P "agHost.*?," test.table //匹配 agHost后带有多个任意字符直到第一个 逗号 结束,-P表示用 perl 的匹配语法,而perl默认是不支持贪婪的 grep --color -o -P "agHost.*?," test.table //-o 只打印匹配部分
匹配数字至少4次
1 2 grep -E ",rows=[0-9]{4,}" grep -E "[0-9]{4,}ms" mongod.log
macOS sed 删除行 1 2 3 4 5 6 7 8 //查找匹配的行:| | | grep -E "\| [[:space:]]*\| [[:space:]]*\|" top_linux_commands.md -B3 //删除行 -i ".bak"是直接操作文件并添加.bak作为备份文件名称,如果不需要备份文件,则使用-i "" sed -i '' -e '/\| [[:space:]]*\| [[:space:]]*\|/d' top_linux_commands.md //先备份文件为.bak, 再删除行 -i ".bak"是添加.bak作为备份文件名称 sed -i '.bak' 's/\| [[:space:]]*\| [[:space:]]*\|/d' top_linux_commands.md
ps 查看进程 1 ps -Tfp pid // -T 展开进程下的线程 -f full -p pid
循环按行处理 1 while read i ; do echo $i ; done <./prometheus.list
3.在以普通用户打开的vim当中保存一个root用户文件
这题目读起来纠结,其实是很常见的,常常忘记了sudo就直接用vim编辑/etc内的文件,(不过也不一定,vim发现保存的文件无法保存时候会提示)等编辑好了,保存时候才发现没权限。曲线方法是先保存个临时文件,退出后再sudo cp回去。不过实际上在vim里面可以直接完成这个过程的,命令就是如此。
查阅vim的文档(输入:help :w),会提到命令:w!{cmd},让vim执行一个外部命令{cmd},然后把当前缓冲区的内容从stdin传入。
tee是一个把stdin保存到文件的小工具。
而%,是vim当中一个只读寄存器的名字,总保存着当前编辑文件的文件路径。
所以执行这个命令,就相当于从vim外部修改了当前编辑的文件,好完工。
4.切换回上一个目录
应该不少人都知道这个,横杆-代表上一个目录的路径。
实际上cd -就是cd $OLDPWD的简写,bash的固定变量$OLDPWD总保存着之前一个目录的路径。
相对地,$PWD总保存着当前目录的路径。这些变量在编写shell脚本时候相当有用。
5.替换上一条命令中的一个短语
又是另外一个事件引用符(event designator),可以把上一条命令当中的foo替换成bar。
在需要重复运行调试一道长长的命令,需要测试某个参数时候,用这个命令会比较实用;但多数人会首先选择按上箭头提出上道命令,再移动光标去修改某参数,这样更直观,但效率上就不够使用引用符高,而且在脚本中用这个方法可以简化很多。
这道命令的原始样式应该是这样的:
本文一开始介绍过!!,后面的一段大家应该很熟悉,vim、sed的替换操作都是这样的语法。
关于事件引用符的更多用法可以深入阅读The Definitive Guide to Bash Command Line History
6.快速备份一个文件
1
$ cp filename**{,.bak }**
这道命令把filename文件拷贝成filename.bak,大家应该在一些比较复杂的安装教程里面见过这样的用法。其原理就在于bash对大括号的展开操作,filename{,.bak}这一段会被展开成filename filename.bak再传给cp,于是就有了备份的命令了。
大括号在bash里面是一个排列的意义,可以试试这个:
1
$ echo {a,b,c }{a,b,c }{a,b,c }
将输出三个集合的全排列:
aaa aab aac aba abb abc aca acb acc
baa bab bac bba bbb bbc bca bcb bcc
caa cab cac cba cbb cbc cca ccb ccc
关于shell当中的集合操作,可深入阅读“Set Operations in the Unix Shell”
7.免密码ssh登录主机
1
$ ssh-copy-id remote-machine
这个命令把当前用户的公钥串写入到远程主机的~/.ssh/authorized_keys内,这样下次使用ssh登录的时候,远程主机就直接根据这串密钥完成身份校验,不再询问密码了。前提是你当前用户有生成了公钥,默认是没有的,先执行ssh-keygen试试吧!
这个命令如果用手工完成,是这样的:
1 2 3
your-machine$ scp ~/.ssh/identity.pub remote-machine: your-machine$ ssh remote-machine remote-machine$ cat identity.pub >> ~/.ssh/authorized_keys
如果你想删掉远程主机上的密钥,直接打开authorized_keys,搜索你的用户名,删除那行,即可。
8.抓取Linux桌面的视频
1
$ ffmpeg -f x11grab -s wxga -r 25 -i :0.0 -sameq **/tmp /**out.mpg
我们在一些视频网站上看到别人的3D桌面怎么怎么酷的视频,通常就是这么来的,ffmpeg可以直接解码X11的图形,并转换到相应输出格式。
ffmpeg的通常用法是,根据一堆参数,输出一个文件,输出文件通常放最后,下面解析下几个参数:
-f x11grab 指定输入类型。因为x11的缓冲区不是普通的视频文件可以侦测格式,必须指定后ffmpeg才知道如何获得输入。
-s wxga 设置抓取区域的大小。wxga是1366*768的标准说法,也可以换成-s 800×600的写法。
-r 25 设置帧率,即每秒抓取的画面数。
-i :0.0 设置输入源,本地X默认在0.0
-sameq 保持跟输入流一样的图像质量,以用来后期处理。
至于其他ffmpeg的用法,可以参考下面两篇文章:
· How to Extract Audio Tracks from YouTube Videos
· Converting YouTube Flash Videos to a Better Format with ffmpeg
后记
说Shell是一种编程语言,可能有些尴尬,虽然很多人每天都在用Shell,但从来没见它荣登TIOBE编程语言排行榜之类的,可以说毫无名分,因为很多用户没意识到它是一种语言,只当做这是一个能够很好完成任务的工具,基本得理所当然,就好像GUI程序的菜单、按钮一样。
掌握Shell,通常能够让任务在数秒钟内完成,这就让Shell跟C、Perl、Python这些语言区别开来,没人否认后者更能胜任更多的任务,但是他们是在不同的层面上去做,Shell依赖大量的系统组件黏合调用,而后者依赖各种库,各所擅长不同的应用领域,比喻就是,Shell是混凝土,可以很方便地粘合一些建筑组件而成为稳固的高楼大厦;但同样是粘合剂,粘玻璃窗、粘书报、粘皮鞋,混凝土是绝对不合适的,Shell并不擅长一些细致操作,比如它连浮点运算都不支持,更别提什么图形运算什么的。但这并不妨碍Shell来帮我们完成很多粗重任务。
Shell的工作方式,大多数入门用户会觉得枯燥难学,而所谓的经典教材也离不开《Advanced Bash-Scripting》、《Bash Guide for Beginners》,但类似本文这样的一些“雕虫小技”因为难登大雅之堂绝不会收录进去。这情况如果象国外一些unix用户比较多的地方会有很好改善,即使是新手,偶尔看看别人的操作都能“偷师”一手,我编译本系列文章其实也就希望稍微改善一下这个状况。
1.用你最喜欢的编辑器来敲命令
1
command <**CTRL-x CTRL-e**>
在已经敲完的命令后按,会打开一个你指定的编辑器(比如vim,通过环境变量$EDITOR指定),里面就是你刚输入的命令,然后爱怎么编辑就怎么编辑吧,特别是那些参数异常复杂的程序,比如mencoder/ffmpeg,一个命令动辄3、4行的,要修改其中的参数,这个方法最合适不过了,保存退出后自动执行这个程序。
实际上这是readline库 的功能,在默认情况下,bash使用的是emacs模式的命令行操作方式,是调用这个功能的一个绑定。如果你习惯使用vi模式,按可以实现同样功能。
如果你喜欢别的编辑器,可以在~/.bashrc里面放上比如export EDITOR=nano的命令。
另外一个修改命令的方法是使用fc命令(Fix Command),在编辑器里面打开上一句命令。我们的第一辑连载 提过一个^foo^bar^命令可以用fc来实现:fc -s foo=bar。
2.清空或创建一个文件
>在shell里面是标准输出重定向符,即把(前部个命令的)命令行输出转往一个文件内,但这里没有“前部命令”,输出为空,于是就覆盖(或创建)成一个空文件了。
有些脚本的写法是:>file.txt,因为:是bash默认存在的空函数。
单纯创建文件也可以用$touch file.txt,touch本来是用作修改文件的时间戳,但如果文件不存在,就自动创建了。
3.用ssh创建端口转发通道
1
ssh -N -L2001:remotehost:80 user**@**somemachine
这个命令在本机打开了2001端口,对本机2001端口的请求通过somemachine作为跳板,转到remotehost的80端口上。
实现效果跟术语反向代理是相似的,实际上就是端口转发,注意上面的描述涉及了3台主机,但当然somemachine可以变成localhost。
这个命令比较抽象,但有时候是很有用的,比如因为众所周知的原因国内的IP的80端口无法使用,又或者公司的防火墙只给外网开了ssh端口,需要访问内部服务器一个web应用,以及需要访问某些限定了来源IP的服务,就可以用上这个方法了。
举一个具体例子,运行:
1 2
ssh -f -N -L 0.0.0.0:443:twitter.com:443 shell.cjb.net ssh -f -N -L 0.0.0.0:80:twitter.com:80 shell.cjb.net
然后在/etc/hosts里面添加127.0.0.1 twitter.com,好吧剩下的你懂的。
当然通常做这个功能的反向代理,应该要用squid、nginx之类,ssh就算是轻量级的尝试吧!
4.重置终端
如果你试过不小心cat了某个二进制文件,很可能整个终端就傻掉了,可能不会换行,没法回显,大堆乱码之类的,这时候敲入reset回车,不管命令有没有显示,就能回复正常了。
实际上reset命令只是输出了一些特殊字符,我们看BusyBox里面最简单的reset程序的实现:
1
printf(“\033 c**\033**(K**\033**[J**\033**[0m**\033**[?25h”);
输出的这些字符对Shell是有特殊意义的:
· \033c: “ESC c” – 发送重置命令;
· \033(K: “ESC ( K” – 重载终端的字符映射;
· \033[J: “ESC [ J” – 清空终端内容;
· \033[0m: “ESC [ 0 m” – 初始化字符显示属性;
· \033[?25h: “ESC [ ? 25 h” – 让光标可见;
其中字符显示属性 经常用来设定打印字符的颜色等,可参考这个博文 。
5.在午夜的时候执行某命令
说的就是at这个组件,通常跟cron相提并论,不过at主要用于定时一次性任务,而cron定时周期性任务。
at的参数比较人性化,跟英语语法一样,可以tomorrow, next week之类的,详细的查看手册man at。
6.远程传送麦克风语音
1
dd if=**/dev /dsp | ssh username @host dd of= /dev /**dsp
没错就是实现一个喊话器的功能。
/dev/dsp是Linux下声卡的文件映射(Digital Signal Proccessor),从其中读数据就是录音,往里面写数据就是播放,相当简单!
dd是常用的数据拷贝程序,如果不同时指定if、of,就直接使用stdin/stdout来传输。
如果你没有远程主机,可以试试这样:
1
dd if=**/dev /dsp of= /dev /**dsp
直接回放麦克风的声音,只是有一点延时。
但是如果有别的程序正在使用声卡,这个方法就不凑效了,因为一般的声卡都不允许多个音频流同时处理,可以借用alsa组件的工具,arecord跟aplay:
1
arecord | ssh username**@**host aplay
本地回放就是:
如果你想吓吓别人:
1
cat **/dev /urandom | ssh username @**host aplay
7.映射一个内存目录
1
mount -t tmpfs -o size=1024m tmpfs **/mnt /**ram
这个命令开了一块1G内存来当目录用。不过放心,如果里面没文件,是不会占用内存的,用多少占多少。
不过一般来说没必要手动挂载,因为多数发行版都会在fstab内预留了一个内存目录,挂载在/dev/shm,直接使用即可;
最常见的用途是用内存空间来放Firefox的配置,可以让慢吞吞的FF快很多,参见Shellex的博文:用tmpfs让Firefox在内存中飞驰 ,以及后来的改进:用tmpfs让Firefox在内存中飞驰II ,其中提到的脚本来自speeding up firefox with tmpfs and automatic rsync 。
那个破烂LinuxQQ也可以用这个方法,减少因为大量磁盘IO导致的问题。
8.用diff对比远程文件跟本地文件
1
ssh user**@**host cat **/path /to /**remotefile | diff **/path /to /**localfile -
diff通常的用法是从参数读入两个文件,而命令里面的-则是指从stdin读入了。
善用ssh可以让web开发减少很多繁琐,还有比如sshfs,可以从编辑 **-上传 编辑 上传 的人工循环里面解脱出来。
9.查看系统中占用端口的进程
Netstat是很常用的用来查看Linux网络系统的工具之一,这个参数可以背下来:
· -t: 显示TCP链接信息
· -u: 显示UDP链接信息
· -l: 显示监听状态的端口
· -n: 直接显示ip,不做名称转换
· -p: 显示相应的进程PID以及名称(要root权限)
如果要查看关于sockets更详细占用信息等,可以使用lsof工具。
1. 更友好的显示当前挂载的文件系统 | 1 | **mount** **|** column -t |
这条命令适用于任何文件系统,column 用于把输出结果进行列表格式化操作,这里最主要的目的是让大家熟悉一下 columnt 的用法。 下面是单单使用 mount 命令的结果:
1``2``3``4``5$ **mount**`` ``**/**dev**/**root on **/** **type** ext3 **(**rw**)**``**/**proc on **/**proc **type** proc **(**rw**)**``**/**dev**/**mapper**/**lvmraid-home on **/**home **type** ext3 **(**rw,noatime**)**
而加了 column -t 命令后就成为这样了:
| 1``2``3``4``5 | $ **mount** **|** column -t`` ``**/**dev**/**root on **/** **type** ext3 **(**rw**)**``**/**proc on **/**proc **type** proc **(**rw**)**``**/**dev**/**mapper**/**lvmraid-home on **/**home **type** ext3 **(**rw,noatime**)** |
另外你可加上列名称来改善输出结果
| 1``2``3``4``5``6 | $ **(echo** "DEVICE - PATH - TYPE FLAGS" **&&** **mount)** **|** column -t`` ``DEVICE - PATH - TYPE FLAGS``**/**dev**/**root on **/** **type** ext3 **(**rw**)**``**/**proc on **/**proc **type** proc **(**rw**)**``**/**dev**/**mapper**/**lvmraid-home on **/**home **type** ext3 **(**rw,noatime**)** |
列2和列4并不是很友好,我们可以用 awk 来再处理一下
| 1``2``3``4``5``6 | $ **(echo** "DEVICE PATH TYPE FLAGS" **&&** **mount** **|** **awk** '$2=$4="";1'**)** **|** column -t`` ``DEVICE PATH TYPE FLAGS``**/**dev**/**root **/** ext3 **(**rw**)**``**/**proc **/**proc proc **(**rw**)**``**/**dev**/**mapper**/**lvmraid-home **/**home ext3 **(**rw,noatime**)** |
最后我们可以设置一个别名,为 nicemount
| 1 | $ nicemount**()** **{** **(echo** "DEVICE PATH TYPE FLAGS" **&&** **mount** **|** **awk** '$2=$4="";1'**)** **|** column -t; **}** |
试一下
1``2``3``4``5``6$ nicemount`` ``DEVICE PATH TYPE FLAGS``**/**dev**/**root **/** ext3 **(**rw**)**``**/**proc **/**proc proc **(**rw**)**``**/**dev**/**mapper**/**lvmraid-home **/**home ext3 **(**rw,noatime**)**
2. 运行前一个 Shell 命令,同时用 “bar” 替换掉命令行中的每一个 “foo”
1**!!**:gs**/**foo**/**bar
!! 表示重复执行上一条命令,并用 :gs/foo/bar 进行替换操作。 关于 !! 这个用法在前一篇文章中 已有详细的介绍。
3. 实时某个目录下查看最新改动过的文件
1**watch** -d -n 1 'df; ls -FlAt /path'
watch 是实时监控工具,-d 参数会高亮显示变化的区域,-n 1 参数表示刷新间隔为 1 秒。 df; ls -FlAt /path 运行了两条命令,df 是输出磁盘使用情况,ls -FlAt 则列出 /path 下面的所有文件。 ls -FlAt 的参数详解:
· -F 在文件后面加一个文件符号表示文件类型,共有 /=>@| 这几种类型, 表示可执行文件,/ 表示目录,= 表示接口( sockets) ,> 表示门, @ 表示符号链接, | 表示管道。
· -l 以列表方式显示
· -A 显示 . 和 ..
· -t 根据时间排序文件
4. 通过 SSH 挂载远程主机上的文件夹
1sshfs name**@**server:**/**path**/**to**/**folder **/**path**/**to**/**mount**/**point
这条命令可以让你通过 SSH 加载远程主机上的文件系统为本地磁盘,前提是你需要安装 FUSE 及 sshfs 这两个软件。 译者注 :关于 sshfs 实际上我之前写过一篇文章介绍过,详见在 Ubuntu 上使用 sshfs 映射远程 ssh 文件系统为本地磁盘 。 卸载的话使用 fusermount 或 umount 命令:
1``2$ fusermount -u **/**path**/**to**/**mount**/**point``*# umount /path/to/mount/point*
5. 通过 DNS 来读取 Wikipedia 的词条
1**dig** +short txt .wp.dg.cx
这也许是最有趣的一条技巧了,David Leadbeater 创建了一个 DNS 服务器 ,通过它当你查询一个 TXT 记录类型时,会返回一条来自于 Wikipedia 的简短的词条文字,这是他的介绍 。 这里有一个样例,来查询 “hacker” 的含义:
1``2``3``4``5``6``7``8$ **dig** +short txt hacker.wp.dg.cx`` ``"Hacker may refer to: Hacker (computer security), someone involved``in computer security/insecurity, Hacker (programmer subculture), a``programmer subculture originating in the US academia in the 1960s,``which is nowadays mainly notable for the free software/” “open``source movement, Hacker (hobbyist), an enthusiastic home computer``hobbyist http://a.vu/w:Hacker"
这里使用了 dig 命令,这是标准的用来查询 DNS 的系统管理工具,+short 参数是让其仅仅返回文字响应,txt 则是指定查询 TXT 记录类型。 更简单的做法是你可以为这个技巧创建一个函数:
1``2``3``4``5wiki**()** **{** **dig** +short txt $1.wp.dg.cx; **}**``*#**然后试试吧:*``wiki hacker`` ``"Hacker may refer to: Hacker (computer security), …"
如果你不想用 dig ,也可以用 host 命令:
1host -t txt hacker.wp.dg.cx
另外在Twitter上看过某人的创意,用普通的dns来作为程序版本更新的查询服务器:设定域名software-version-check.example.com的A记录为1.2.40.3,对比自己的版本号,嗯,有更新了!
6. 用 Wget 的递归方式下载整个网站 1 nohup wget --random-wait -nc -q -r -l 0 --reject=html -np -e robots=off -U Mozilla www.example.com &
参数解释: –random-wait 等待 0.5 到 1.5 秒的时间来进行下一次请求 -r 开启递归检索 -e robots=off 忽略 robots.txt -U Mozilla 设置 User-Agent 头为 Mozilla 其它一些有用的参数:
· –limit-rate=20K 限制下载速度为 20K
· -o logfile.txt 记录下载日志
· -l 0 删除深度(默认为5)
· -wait=1h 每下载一个文件后等待1小时
-np 不下载父目录
–reject=html 不下载html
-nc 本地已有的不再下载
7. 复制最后使用的命令中的参数 1 2 Ctrl + . or ESC + . command + . //macOS
这个快捷键只能工作于 shell 的 emacs 编辑模式,它可以从最后使用的命令行中复制参数到当前命令行中,下面是一个样例:
1``2``3``4``5$ **echo** a b c``a b c`` ``$ **echo**``$ **echo** c
你可以重复执行该快捷键,以便获取自已需要的参数, 以下是样例:
1``2``3``4``5``6``7``8``9``10$ **echo** 1 2 3``1 2 3``$ **echo** a b c``a b c`` ``$ **echo**``$ **echo** c`` ``$ **echo** again``$ **echo** 3
另外,假如你想指定第1个或第2个,或者是第 n 个参数的话,可以按 ALT + 1 (或 ESC + 1) 或 ALT + 2 (或 ESC +2) 这样形式的快捷键。 以下是样例:
1``2``3``4``5``6``7``8``9``10$ **echo** a b c``a b c`` ``$ **echo**``$ **echo** a``a`` ``$ **echo**``$ **echo** b``b
查看Emacs Editing Mode Keyboard Shortcuts 一文获取更多类似的快捷键。
8. 执行一条命令但不保存到 history 中
这条命令可运行于最新的 Bash shell 里,在其它 shell 中没测试过。 通过在命令行前面添加一个空格,就可以阻止这条命令被保存到 bash history (~/.bash_history) 文件中,这个行为可以通过 $HISTIGNORE shell 变量来控制。我的设置是 HISTIGNORE=”&:[ ]*” ,表示不保存重复的命令到 history 中,并且不保存以空格开头的命令行。$HISTIGNORE 中的值以冒号分隔。 如果你的命令内包含密码,比如mysqladmin,不把它记录在历史当中是好主义。 深入了解的话,可进一步看此文The Definitive Guide to Bash Command Line History
9. 显示当前目录中所有子目录的大小 du
sudo du –max-depth=1 -BG //单位 block-size G; or -BM MB
du -h –max-depth=1
–max-depth=1 参数可以让 du 命令显示当前目录下 1 级子目录的统计信息,当然你也可以把 1 改为 2 ,进一步显示 2 级子目录的统计信息,可以灵活运用。而 -h 参数则是以 Mb 、G 这样的单位来显示大小。 译者注 :在此推荐一个小工具 ncdu ,可以更方便的达到此效果。
按单位大小排序
1 2 3 4 5 6 7 8 9 10 11 #du -sh * | sort -hr | head 1.8T anolis_yum 1.6T u02 1.5T os 45G drds_image 23G polarx 8.3G src 7.9G drds.pcap 7.8G root 4.3G core.24086 3.5G core.112462
10. 显示消耗内存最多的 10 个运行中的进程,以内存使用量排序 | 1 | **ps** aux **|** **sort** -nk +4 **|** **tail** |
显然这并不是最好的方法,但它确实用起还不错。 这是一个典型的管道应用,通过 ps aux 来输出到 sort 命令,并用 sort 排序列出 4 栏,再进一步转到 tail 命令,最终输出 10 行显示使用内存最多的进程情况。 假如想要发现哪个进程使用了大量内存的话,我通常会使用 htop 或 top 而非 ps 。
11. 用 python 快速开启一个 SMTP 服务
1python -m smtpd -n -c DebuggingServer localhost:1025
这是一个用 Python 标准库 smtpd (用 -m smtpd 指定) 实现在简易 SMTP 服务,运行于 1025 端口 。 另外三个参数的解释: -n 参数让 Python 不要进行 setuid ( 改变用户)为 “nobody” ,也就是说直接用你的帐号来运行 -c DebuggingServer 参数是让 Python 运行时在屏幕上输出调试及运行信息 * localhost:1025 参数则是让 Python 在本地的 1025 端口上开启 SMTP 服务 另外,假如你想让程序运行于标准的 25 的端口上的话,你必须使用 sudo 命令,因为只有 root 才能在 1-1024 端口上开启服务。如下:
1**sudo** python -m smtpd -n -c DebuggingServer localhost:25
1.查看ascii码表
很多人初学编程都会接触到ascii码的概念,有时候为了查某个符号的ascii值,可能还得翻箱倒柜找出当年的课本?Linux Manpage 里面其实包含了很多类似的实用资料,上述命令就能很详细的方式解释ascii编码,当然这里还有在线版 。
man命令的第二个参数是区域码,用来区分索引词的范围,比如printf,在C标准库里面的printf跟bash当中的printf是不同的,前者的查询是man 3 printf,后者是man 1 printf。如果这个区域码省略,就会从1开始搜索,直到找到为止。
命令man man可以看到详细的解释 。
manpages里面还有一些有趣而且实用的资料,可能鲜为人知:
· man 1 intro – 一篇对从未接触过Linux的用户的简明教程。
· man 2 syscalls – 内核系统请求的列表,按内核版本注释分类,系统编程必备。
· man 2 select_tut – 关于select()系统请求的教程。
· man 3 string – 在头文件内的所有函数。
· man 3 stdio – 关于头文件的使用,标准输入/输出库的说明。
· man 3 errno – 所有errorno的取值及说明。(C语言内类似其他语言的异常告知机制)
· man 4 console_codes – Linux的终端控制码及其使用解释。
· man 4 full – 介绍/dev/full这个总是处于“满”状态的磁盘。(对应/dev/null这个总是空的设备)
· man 5 proc – 介绍/proc下的文件系统。
· man 5 filesystems – 各种Linux文件系统。
第7区里面的资料通常最酷:
· man 7 bootparam – 详细解释内核启动参数。
· man 7 charsets – 解释各种语言的编码集。(gbk,gb2312等)
· man 7 glob – 解释glob文件名管理机制的工作过程。
· man 7 hier – 解释Linux文件系统结构各个部分的作用。
· man 7 operator – C语言的运算符的列表。
· man 7 regex – 介绍正则表达式。
· man 7 suffixes – 常见文件后缀名的列表跟解释。
· man 7 time – Linux的时钟机制解释。
· man 7 units – 数值单位及其数值的解释。
· man 7 utf8 – 描述UTF-8编码。
· man 7 url – 解释URL、URI、URN等的标准。
2.简易计时器
运行命令开始算起,到结束时按一下Enter,就显示出整个过程的时间,精确到ms级别。
time是用来计算一个进程在运行到结束过程耗费多少时间的程序,它的输出通常有三项:
1 2 3 4 5
$ time ls /opt … real 0m0.008s user 0m0.003s sys 0m0.007s
real指整个程序对真实世界而言运行所需时间,user指程序在用户空间运行的时间,sys指程序对系统调用锁占用时间。
read本来是一个读取用户输入的命令,常见用法是read LINE,用户输入并回车后,键入的内容就被保存到$LINE变量内,但在键入回车前,这个命令是一直阻塞的。
可见time read这命令灵活地利用了操作系统的阻塞。用这个命令来测试一壶水多久煮滚应该是不错的。
3.远程关掉一台Windows机器
1
net rpc shutdown -I IP_ADDRESS -U username**%**password
Windows平台上的net命令是比较强大的,因为其后台是一个RPC类的系统服务,大家应该看过win下用net use \ip\ipc$ *这样一个命令建立IPC空连接,入侵主机的事情。
Linux下的net命令是samba组件的程序,通常包含在smbclient内,可以跟windows主机的文件、打印机共享等服务进行通讯,但是也支持rpc命令。
上述命令就是在远程Windows主机上执行了shutdown命令。当然这不一定成功,关系到win主机上面的安全设置。net命令能够控制到win主机就是了。
4.在一个子shell中运行一个命令
当然这只是演示,要查看目录当然可以ls /tmp。
好处就是不会改变当前shell的目录,以及如果命令中设计环境变量,也不会对当前shell有任何修改。
在Shell编程中还有很多使用上引号来括住一个命令:ls /tmp,这也是子shell过程。可是上引号的方法无法嵌套,而使用小括号的方法可以,一个比较纠结的例子是:
1
echo $(echo -e \x$(printf “%x” 65**))**
5.利用中间管道嵌套使用SSH
1
ssh -t host_A ssh host_B
如果目标机器host_B处于比较复杂的网络环境,本机无法直接访问,但另外一台host_A能够访问到host_B,而且也能被本机访问到,那上述命令就解决了方便登录host_B的问题。
但理论上这个过程是可以无限嵌套的,比如:
1
ssh -t host1 ssh -t host2 ssh -t host3 ssh -t host4 …
嗯那神马FBI CIA的,有本事来捉我吧~
6.清空屏幕
这个跟之前介绍的reset命令重置终端的作用有些类似,其实都只是发送一段控制序列,让终端的显示复位。
还可以这样运行:
tput是专门用来控制终端的一个小工具,也挺强大的,详细信息运行man tput查看。
7.我想知道一台服务器什么时候重启完
系统管理员最常做的事情是重启系统。但是服务器的重启过程往往得花上好几分钟,什么你的服务器4个scsi卡?16个硬盘?系统是Redhat?还完全安装所有组件?好吧,它重启的时间都够你吃顿饭了,所以我很想知道它什么时候回来。
ping命令有个audible ping参数,-a,当它终于ping通你的服务器时会让小喇叭叫起来。
8.列出你最常用的10条命令
1
history | awk ‘{a[$2]++}END{for(i in a){print a[i] “ “ i}}’ | sort -rn | head
这行命令组合得很妙:
history输出用户了命令历史;awk统计并输出列表;sort排序;head截出前10行。
9.检查Gmail新邮件
1 2 3 4 5 6
curl -u you**@**gmail.com –silent “https://mail.google.com/mail/feed/atom “ | perl -ne \ ‘ print “Subject: $1 “ if /(.+?)</title>/ && $title++; print “(from $1)\n” if /<email>(.+?)</email>/; ‘</th>
</tr>
</thead>
</table>
<p>Gmail的一个特色是支持Atom feed输出邮件列表,所以总是见到很多Gmail邮件提醒器之类的,因为开发特简单,atom很方便。</p>
<p>这里只是利用了perl的正则来解析atom(sed/awk也能做到)。</p>
<h2 id="10-用Telnet看《星球大战》"><a href="#10-用Telnet看《星球大战》" class="headerlink" title="10.用Telnet看《星球大战》"></a>10.用Telnet看《星球大战》</h2><table>
<thead>
<tr>
<th>1</th>
<th>telnet towel.blinkenlights.nl</th>
</tr>
</thead>
</table>
<p>没什么好解释的,就是ASCII艺术之一。如果你有ipv6连接,还能看到彩色版的。牛吧?</p>
</div>
<footer class="post-footer">
<div class="post-eof"></div>
</footer>
</article>
</div>
<div class="post-block">
<article itemscope itemtype="http://schema.org/Article" class="post-content" lang="">
<link itemprop="mainEntityOfPage" href="https://plantegg.github.io/2016/10/12/ss%E7%94%A8%E6%B3%95%E5%A4%A7%E5%85%A8/">
<span hidden itemprop="author" itemscope itemtype="http://schema.org/Person">
<meta itemprop="image" content="/images/avatar.gif">
<meta itemprop="name" content="twitter @plantegg">
</span>
<span hidden itemprop="publisher" itemscope itemtype="http://schema.org/Organization">
<meta itemprop="name" content="plantegg">
<meta itemprop="description" content="java mysql tcp performance network docker Linux">
</span>
<span hidden itemprop="post" itemscope itemtype="http://schema.org/CreativeWork">
<meta itemprop="name" content=" | plantegg">
<meta itemprop="description" content="">
</span>
<header class="post-header">
<h2 class="post-title" itemprop="name headline">
<a href="/2016/10/12/ss%E7%94%A8%E6%B3%95%E5%A4%A7%E5%85%A8/" class="post-title-link" itemprop="url">就是要你懂网络监控--ss用法大全</a>
</h2>
<div class="post-meta-container">
<div class="post-meta">
<span class="post-meta-item">
<span class="post-meta-item-icon">
<i class="far fa-calendar"></i>
</span>
<span class="post-meta-item-text">发表于</span>
<time title="创建时间:2016-10-12 15:30:03" itemprop="dateCreated datePublished" datetime="2016-10-12T15:30:03+08:00">2016-10-12</time>
</span>
<span class="post-meta-item">
<span class="post-meta-item-icon">
<i class="far fa-calendar-check"></i>
</span>
<span class="post-meta-item-text">更新于</span>
<time title="修改时间:2025-11-29 15:11:18" itemprop="dateModified" datetime="2025-11-29T15:11:18+08:00">2025-11-29</time>
</span>
<span class="post-meta-item">
<span class="post-meta-item-icon">
<i class="far fa-folder"></i>
</span>
<span class="post-meta-item-text">分类于</span>
<span itemprop="about" itemscope itemtype="http://schema.org/Thing">
<a href="/categories/network/" itemprop="url" rel="index"><span itemprop="name">network</span></a>
</span>
</span>
</div>
</div>
</header>
<div class="post-body" itemprop="articleBody">
<h1 id="就是要你懂网络监控–ss用法大全"><a href="#就是要你懂网络监控–ss用法大全" class="headerlink" title="就是要你懂网络监控–ss用法大全"></a>就是要你懂网络监控–ss用法大全</h1><p>ss是Socket Statistics的缩写。</p>
<p>netstat命令大家肯定已经很熟悉了,但是在2001年的时候netstat 1.42版本之后就没更新了,之后取代的工具是ss命令,是iproute2 package的一员。</p>
<blockquote>
<p> rpm -ql iproute | grep ss<br> /usr/sbin/ss</p>
</blockquote>
<p>netstat的替代工具是nstat,当然netstat的大部分功能ss也可以替代</p>
<p>ss可以显示跟netstat类似的信息,但是速度却比netstat快很多,netstat是基于/proc/net/tcp获取 TCP socket 的相关统计信息,用strace跟踪一下netstat查询tcp的连接,会看到他open的是/proc/net/tcp的信息。ss快的秘密就在于它利用的是TCP协议的tcp_diag模块,而且是从内核直接读取信息,<strong>当内核不支持 tcp_diag 内核模块时,会回退到 /proc/net/tcp 模式</strong>。</p>
<p>/proc/net/snmp 存放的是系统启动以来的累加值,netstat -s 读取它<br>/proc/net/tcp 是存放目前活跃的tcp连接的统计值,连接断开统计值清空, ss -it 读取它</p>
<h2 id="ss-查看Buffer窗口"><a href="#ss-查看Buffer窗口" class="headerlink" title="ss 查看Buffer窗口"></a><a target="_blank" rel="noopener" href="https://access.redhat.com/discussions/3624151">ss 查看Buffer窗口</a></h2><p>ss参数说明<a target="_blank" rel="noopener" href="https://man7.org/linux/man-pages/man8/ss.8.html">权威参考</a></p>
<figure class="highlight shell"><table><tr><td class="gutter"><pre><span class="line">1</span><br><span class="line">2</span><br><span class="line">3</span><br><span class="line">4</span><br><span class="line">5</span><br><span class="line">6</span><br><span class="line">7</span><br><span class="line">8</span><br><span class="line">9</span><br><span class="line">10</span><br><span class="line">11</span><br><span class="line">12</span><br><span class="line">13</span><br><span class="line">14</span><br><span class="line">15</span><br><span class="line">16</span><br><span class="line">17</span><br><span class="line">18</span><br><span class="line">19</span><br><span class="line">20</span><br><span class="line">21</span><br><span class="line">22</span><br><span class="line">23</span><br><span class="line">24</span><br><span class="line">25</span><br><span class="line">26</span><br><span class="line">27</span><br><span class="line">28</span><br><span class="line">29</span><br><span class="line">30</span><br><span class="line">31</span><br><span class="line">32</span><br><span class="line">33</span><br><span class="line">34</span><br><span class="line">35</span><br><span class="line">36</span><br><span class="line">37</span><br><span class="line">38</span><br><span class="line">39</span><br><span class="line">40</span><br><span class="line">41</span><br><span class="line">42</span><br><span class="line">43</span><br><span class="line">44</span><br><span class="line">45</span><br><span class="line">46</span><br><span class="line">47</span><br></pre></td><td class="code"><pre><span class="line">-m, --memory //查看每个连接的buffer使用情况</span><br><span class="line"> Show socket memory usage. The output format is:</span><br><span class="line"></span><br><span class="line"> skmem:(r<rmem_alloc>,rb<rcv_buf>,t<wmem_alloc>,tb<snd_buf>,</span><br><span class="line"> f<fwd_alloc>,w<wmem_queued>,o<opt_mem>,</span><br><span class="line"> bl<back_log>,d<sock_drop>)</span><br><span class="line"></span><br><span class="line"> <rmem_alloc></span><br><span class="line"> the memory allocated for receiving packet</span><br><span class="line"></span><br><span class="line"> <rcv_buf></span><br><span class="line"> the total memory can be allocated for receiving</span><br><span class="line"> packet</span><br><span class="line"></span><br><span class="line"> <wmem_alloc></span><br><span class="line"> the memory used for sending packet (which has been</span><br><span class="line"> sent to layer 3)</span><br><span class="line"></span><br><span class="line"> <snd_buf></span><br><span class="line"> the total memory can be allocated for sending</span><br><span class="line"> packet</span><br><span class="line"></span><br><span class="line"> <fwd_alloc></span><br><span class="line"> the memory allocated by the socket as cache, but</span><br><span class="line"> not used for receiving/sending packet yet. If need</span><br><span class="line"> memory to send/receive packet, the memory in this</span><br><span class="line"> cache will be used before allocate additional</span><br><span class="line"> memory.</span><br><span class="line"></span><br><span class="line"> <wmem_queued></span><br><span class="line"> The memory allocated for sending packet (which has</span><br><span class="line"> not been sent to layer 3)</span><br><span class="line"></span><br><span class="line"> <ropt_mem></span><br><span class="line"> The memory used for storing socket option, e.g.,</span><br><span class="line"> the key for TCP MD5 signature</span><br><span class="line"></span><br><span class="line"> <back_log></span><br><span class="line"> The memory used for the sk backlog queue. On a</span><br><span class="line"> process context, if the process is receiving</span><br><span class="line"> packet, and a new packet is received, it will be</span><br><span class="line"> put into the sk backlog queue, so it can be</span><br><span class="line"> received by the process immediately</span><br><span class="line"></span><br><span class="line"> <sock_drop></span><br><span class="line"> the number of packets dropped before they are de-</span><br><span class="line"> multiplexed into the socket</span><br></pre></td></tr></table></figure>
<p>The entire print format of <code>ss -m</code> is given in the source:</p>
<figure class="highlight plaintext"><table><tr><td class="gutter"><pre><span class="line">1</span><br><span class="line">2</span><br><span class="line">3</span><br><span class="line">4</span><br><span class="line">5</span><br><span class="line">6</span><br><span class="line">7</span><br><span class="line">8</span><br><span class="line">9</span><br><span class="line">10</span><br><span class="line">11</span><br><span class="line">12</span><br><span class="line">13</span><br><span class="line">14</span><br><span class="line">15</span><br><span class="line">16</span><br><span class="line">17</span><br><span class="line">18</span><br><span class="line">19</span><br><span class="line">20</span><br><span class="line">21</span><br><span class="line">22</span><br><span class="line">23</span><br><span class="line">24</span><br><span class="line">25</span><br><span class="line">26</span><br><span class="line">27</span><br><span class="line">28</span><br><span class="line">29</span><br><span class="line">30</span><br><span class="line">31</span><br><span class="line">32</span><br><span class="line">33</span><br><span class="line">34</span><br><span class="line">35</span><br></pre></td><td class="code"><pre><span class="line"> printf(" skmem:(r%u,rb%u,t%u,tb%u,f%u,w%u,o%u",</span><br><span class="line"> skmeminfo[SK_MEMINFO_RMEM_ALLOC],</span><br><span class="line"> skmeminfo[SK_MEMINFO_RCVBUF],</span><br><span class="line"> skmeminfo[SK_MEMINFO_WMEM_ALLOC],</span><br><span class="line"> skmeminfo[SK_MEMINFO_SNDBUF],</span><br><span class="line"> skmeminfo[SK_MEMINFO_FWD_ALLOC],</span><br><span class="line"> skmeminfo[SK_MEMINFO_WMEM_QUEUED],</span><br><span class="line"> skmeminfo[SK_MEMINFO_OPTMEM]);</span><br><span class="line"></span><br><span class="line"> if (RTA_PAYLOAD(tb[attrtype]) >=</span><br><span class="line"> (SK_MEMINFO_BACKLOG + 1) * sizeof(__u32))</span><br><span class="line"> printf(",bl%u", skmeminfo[SK_MEMINFO_BACKLOG]);</span><br><span class="line"></span><br><span class="line"> if (RTA_PAYLOAD(tb[attrtype]) >=</span><br><span class="line"> (SK_MEMINFO_DROPS + 1) * sizeof(__u32))</span><br><span class="line"> printf(",d%u", skmeminfo[SK_MEMINFO_DROPS]);</span><br><span class="line"></span><br><span class="line"> printf(")");</span><br><span class="line"> </span><br><span class="line"> </span><br><span class="line">net/core/sock.c line:3095</span><br><span class="line">void sk_get_meminfo(const struct sock *sk, u32 *mem)</span><br><span class="line">{</span><br><span class="line"> memset(mem, 0, sizeof(*mem) * SK_MEMINFO_VARS);</span><br><span class="line"></span><br><span class="line"> mem[SK_MEMINFO_RMEM_ALLOC] = sk_rmem_alloc_get(sk);</span><br><span class="line"> mem[SK_MEMINFO_RCVBUF] = sk->sk_rcvbuf;</span><br><span class="line"> mem[SK_MEMINFO_WMEM_ALLOC] = sk_wmem_alloc_get(sk);</span><br><span class="line"> mem[SK_MEMINFO_SNDBUF] = sk->sk_sndbuf;</span><br><span class="line"> mem[SK_MEMINFO_FWD_ALLOC] = sk->sk_forward_alloc;</span><br><span class="line"> mem[SK_MEMINFO_WMEM_QUEUED] = sk->sk_wmem_queued;</span><br><span class="line"> mem[SK_MEMINFO_OPTMEM] = atomic_read(&sk->sk_omem_alloc);</span><br><span class="line"> mem[SK_MEMINFO_BACKLOG] = sk->sk_backlog.len;</span><br><span class="line"> mem[SK_MEMINFO_DROPS] = atomic_read(&sk->sk_drops);</span><br><span class="line">}</span><br></pre></td></tr></table></figure>
<p><img src="/images/951413iMgBlog/image-20210604120011898.png" alt="image-20210604120011898"></p>
<p>–memory/-m : 展示buffer窗口的大小</p>
<figure class="highlight plaintext"><table><tr><td class="gutter"><pre><span class="line">1</span><br><span class="line">2</span><br><span class="line">3</span><br><span class="line">4</span><br><span class="line">5</span><br><span class="line">6</span><br><span class="line">7</span><br><span class="line">8</span><br><span class="line">9</span><br><span class="line">10</span><br><span class="line">11</span><br><span class="line">12</span><br><span class="line">13</span><br></pre></td><td class="code"><pre><span class="line">#ss -m | xargs -L 1 | grep "ESTAB" | awk '{ if($3>0 || $4>0) print $0 }'</span><br><span class="line">tcp ESTAB 0 31 10.97.137.1:7764 10.97.137.2:41019 skmem:(r0,rb7160692,t0,tb87040,f1792,w2304,o0,bl0)</span><br><span class="line">tcp ESTAB 0 193 ::ffff:10.97.137.1:sdo-tls ::ffff:10.97.137.2:55545 skmem:(r0,rb369280,t0,tb87040,f1792,w2304,o0,bl0)</span><br><span class="line">tcp ESTAB 0 65 ::ffff:10.97.137.1:splitlock ::ffff:10.97.137.2:47796 skmem:(r0,rb369280,t0,tb87040,f1792,w2304,o0,bl0)</span><br><span class="line">tcp ESTAB 0 80 ::ffff:10.97.137.1:informer ::ffff:10.97.137.3:49279 skmem:(r0,rb369280,t0,tb87040,f1792,w2304,o0,bl0)</span><br><span class="line">tcp ESTAB 0 11 ::ffff:10.97.137.1:acp-policy ::ffff:10.97.137.2:41607 skmem:(r0,rb369280,t0,tb87040,f1792,w2304,o0,bl0)</span><br><span class="line"></span><br><span class="line">#ss -m -n | xargs -L 1 | grep "tcp EST" | grep "t[1-9]"</span><br><span class="line">tcp ESTAB 0 281 10.97.169.173:32866 10.97.170.220:3306 skmem:(r0,rb4619516,t2304,tb87552,f1792,w2304,o0,bl0)</span><br><span class="line"></span><br><span class="line">//如下w204312都很大,接近 tb 大小了,应用代码中写死了 buffer 为 102K</span><br><span class="line">skmem:(r2304,rb204800,t0,tb204800,f18664,w204312,o0,bl0,d40150) cubic wscale:1,1 rto:330 rtt:129.991/0.028 ato:40 mss:1448 rcvmss:536 advmss:1448 cwnd:47 ssthresh:26 bytes_acked:1859972764 bytes_received:8052067 segs_out:1418895 segs_in:635234 send 4.2Mbps lastsnd:84 lastrcv:1035 lastack:84 pacing_rate 8.4Mbps unacked:38 retrans:0/577 rcv_rtt:34871 rcv_space:52040</span><br><span class="line">skmem:(r0,rb204800,t0,tb204800,f1532,w240132,o0,bl0,d40051) cubic wscale:1,1 rto:334 rtt:133.523/0.594 ato:40 mss:1448 rcvmss:536 advmss:1448 cwnd:49 ssthresh:30 bytes_acked:8280788253 bytes_received:55404796 segs_out:6521018 segs_in:2842524 send 4.3Mbps lastsnd:5 lastrcv:7 lastack:88 pacing_rate 8.5Mbps unacked:41 retrans:0/40 reordering:8 rcv_rtt:26793 rcv_space:36790</span><br></pre></td></tr></table></figure>
<p><img src="/images/oss/4a09503e6c6e84c25e026248a1b3ebb6.png" alt="image.png"></p>
<p>如上图,tb指可分配的发送buffer大小,不够还可以动态调整(应用没有写死的话),w[The memory allocated for sending packet (which has not been sent to layer 3)]已经预分配好了的size,t[the memory used for sending packet (which has been sent to layer 3)] , 似乎 w总是等于大于t?</p>
<p>example:</p>
<p><img src="/images/oss/4ed3d8aab6ef3ee45decda75e534baab.png" alt="image.png"></p>
<p>对172.16.210.17和172.16.160.1之间的带宽限速50MB后观察(带宽限制后,发送buffer就很容易被撑满了):</p>
<figure class="highlight shell"><table><tr><td class="gutter"><pre><span class="line">1</span><br><span class="line">2</span><br><span class="line">3</span><br><span class="line">4</span><br><span class="line">5</span><br><span class="line">6</span><br><span class="line">7</span><br><span class="line">8</span><br><span class="line">9</span><br><span class="line">10</span><br><span class="line">11</span><br><span class="line">12</span><br><span class="line">13</span><br><span class="line">14</span><br><span class="line">15</span><br><span class="line">16</span><br><span class="line">17</span><br><span class="line">18</span><br><span class="line">19</span><br><span class="line">20</span><br><span class="line">21</span><br><span class="line">22</span><br><span class="line">23</span><br><span class="line">24</span><br><span class="line">25</span><br><span class="line">26</span><br><span class="line">27</span><br><span class="line">28</span><br><span class="line">29</span><br><span class="line">30</span><br><span class="line">31</span><br><span class="line">32</span><br><span class="line">33</span><br><span class="line">34</span><br><span class="line">35</span><br></pre></td><td class="code"><pre><span class="line"><span class="meta prompt_">$</span><span class="language-bash">ss -m | xargs -L 1 | grep <span class="string">"tcp EST"</span> | awk <span class="string">'{ if($3>0 || $4>0) print $0 }'</span></span></span><br><span class="line">Netid State Recv-Q Send-Q Local Address:Port Peer Address:Port</span><br><span class="line">tcp ESTAB 1431028 0 172.16.210.17:30082 172.16.160.1:4847 skmem:(r2066432,rb2135508,t0,tb46080,f2048,w0,o0,bl0,d72)</span><br><span class="line">tcp ESTAB 1195628 0 172.16.210.17:30086 172.16.160.1:4847 skmem:(r1742848,rb1915632,t8,tb46080,f190464,w0,o0,bl0,d187)</span><br><span class="line">tcp ESTAB 86416 0 172.16.210.17:40470 172.16.160.1:4847 skmem:(r127232,rb131072,t0,tb46080,f3840,w0,o0,bl0,d16)</span><br><span class="line">tcp ESTAB 1909826 0 172.16.210.17:40476 172.16.160.1:4847 skmem:(r2861568,rb2933688,t2,tb46080,f26112,w0,o0,bl0,d15)</span><br><span class="line">tcp ESTAB 758312 0 172.16.210.17:40286 172.16.160.1:4847 skmem:(r1124864,rb1177692,t0,tb46080,f1536,w0,o0,bl0,d17)</span><br><span class="line">tcp ESTAB 2238720 0 172.16.210.17:40310 172.16.160.1:4847 skmem:(r3265280,rb3334284,t0,tb46080,f3328,w0,o0,bl0,d30)</span><br><span class="line">tcp ESTAB 88172 0 172.16.210.17:40508 172.16.160.1:4847 skmem:(r128000,rb131072,t0,tb46080,f3072,w0,o0,bl0,d16)</span><br><span class="line">tcp ESTAB 87700 0 172.16.210.17:41572 172.16.160.1:4847 skmem:(r130560,rb131072,t0,tb46080,f512,w0,o0,bl0,d10)</span><br><span class="line">tcp ESTAB 4147293 0 172.16.210.17:40572 172.16.160.1:4847 skmem:(r6064896,rb6291456,t2,tb46080,f75008,w0,o0,bl0,d27)</span><br><span class="line">tcp ESTAB 1610940 0 172.16.210.17:30100 172.16.160.1:4847 skmem:(r2358784,rb2533092,t6,tb46080,f82432,w0,o0,bl0,d304)</span><br><span class="line">tcp ESTAB 4216156 0 172.16.210.17:30068 172.16.160.1:4847 skmem:(r6091008,rb6291456,t0,tb46080,f3840,w0,o0,bl0,d112)</span><br><span class="line">tcp ESTAB 87468 0 172.16.210.17:40564 172.16.160.1:4847 skmem:(r127232,rb131072,t0,tb46080,f3840,w0,o0,bl0,d16)</span><br><span class="line">tcp ESTAB 0 84608 172.16.210.17:3306 10.100.7.27:43114 skmem:(r0,rb65536,t8352,tb131072,f75648,w92288,o0,bl0,d0)</span><br><span class="line">tcp ESTAB 4141872 0 172.16.210.17:40584 172.16.160.1:4847 skmem:(r6050560,rb6291456,t2,tb46080,f19712,w0,o0,bl0,d14)</span><br><span class="line"><span class="meta prompt_"></span></span><br><span class="line"><span class="meta prompt_">$</span><span class="language-bash">ss -itn</span></span><br><span class="line">State Recv-Q Send-Q Local Address:Port Peer Address:Port</span><br><span class="line">ESTAB 965824 0 172.16.210.17:19310 172.16.160.1:4847</span><br><span class="line"> cubic wscale:9,7 rto:215 rtt:14.405/0.346 ato:160 mss:1440 rcvmss:1460 advmss:1460 cwnd:10 bytes_acked:1324584 bytes_received:2073688144 segs_out:91806 segs_in:1461520 data_segs_out:4824 data_segs_in:1456130 send 8.0Mbps lastsnd:545583 lastrcv:545276 lastack:13173 pacing_rate 16.0Mbps delivery_rate 8.9Mbps app_limited busy:9071ms rcv_rtt:1.303 rcv_space:164245 minrtt:1.293</span><br><span class="line">ESTAB 0 84371 172.16.210.17:3306 10.100.7.147:59664</span><br><span class="line"> cubic wscale:7,7 rto:217 rtt:16.662/0.581 ato:40 mss:1448 rcvmss:976 advmss:1448 cwnd:375 ssthresh:19 bytes_acked:5087795046 bytes_received:1647 segs_out:3589314 segs_in:358086 data_segs_out:3589313 data_segs_in:8 send 260.7Mbps lastsnd:6 lastrcv:1177745 lastack:4 pacing_rate 312.8Mbps delivery_rate 32.9Mbps busy:1176476ms rwnd_limited:1717ms(0.1%) sndbuf_limited:159867ms(13.6%) unacked:37 retrans:0/214 rcv_space:14600 notsent:32055 minrtt:7.945</span><br><span class="line">ESTAB 0 83002 172.16.210.17:3306 10.100.7.28:34066</span><br><span class="line"> cubic wscale:7,7 rto:215 rtt:14.635/0.432 ato:40 mss:1448 rcvmss:976 advmss:1448 cwnd:144 ssthresh:144 bytes_acked:972464708 bytes_received:1466 segs_out:671667 segs_in:94369 data_segs_out:671666 data_segs_in:8 send 114.0Mbps lastsnd:1 lastrcv:453365 lastack:1 pacing_rate 136.8Mbps delivery_rate 24.0Mbps busy:453493ms sndbuf_limited:200ms(0.0%) unacked:23 rcv_space:14600 notsent:49698 minrtt:9.937</span><br><span class="line">ESTAB 1239616 0 172.16.210.17:41592 172.16.160.1:4847</span><br><span class="line"> cubic wscale:9,7 rto:216 rtt:15.754/0.775 ato:144 mss:1440 rcvmss:1460 advmss:1460 cwnd:10 bytes_acked:20321 bytes_received:1351071 segs_out:269 segs_in:1091 data_segs_out:76 data_segs_in:988 send 7.3Mbps lastsnd:339339 lastrcv:337401 lastack:10100 pacing_rate 14.6Mbps delivery_rate 1.0Mbps app_limited busy:1214ms rcv_rtt:227.156 rcv_space:55581 minrtt:11.38</span><br><span class="line">ESTAB 3415748 0 172.16.210.17:30090 172.16.160.1:4847</span><br><span class="line"> cubic wscale:9,7 rto:202 rtt:1.667/0.011 ato:80 mss:1440 rcvmss:1460 advmss:1460 cwnd:10 bytes_acked:398583 bytes_received:613824362 segs_out:28630 segs_in:437621 data_segs_out:1495 data_segs_in:435792 send 69.1Mbps lastsnd:1179931 lastrcv:1179306 lastack:12149 pacing_rate 138.2Mbps delivery_rate 7.2Mbps app_limited busy:2520ms rcv_rtt:1.664 rcv_space:212976 minrtt:1.601</span><br><span class="line">ESTAB 86480 0 172.16.210.17:41482 172.16.160.1:4847</span><br><span class="line"> cubic wscale:9,7 rto:215 rtt:14.945/1.83 ato:94 mss:1440 rcvmss:1460 advmss:1460 cwnd:10 bytes_acked:3899 bytes_received:93744 segs_out:73 segs_in:136 data_segs_out:20 data_segs_in:83 send 7.7Mbps lastsnd:449541 lastrcv:449145 lastack:19314 pacing_rate 15.4Mbps delivery_rate 964.2Kbps app_limited busy:296ms rcv_rtt:8561.27 rcv_space:14600 minrtt:11.948</span><br><span class="line">ESTAB 89136 0 172.16.210.17:40480 172.16.160.1:4847</span><br><span class="line"> cubic wscale:9,7 rto:213 rtt:12.11/0.79 ato:196 mss:1440 rcvmss:1460 advmss:1460 cwnd:10 bytes_acked:2510 bytes_received:95652 segs_out:102 segs_in:168 data_segs_out:16 data_segs_in:81send 9.5Mbps lastsnd:1099067 lastrcv:1098659 lastack:13686 pacing_rate 19.0Mbps delivery_rate 1.0Mbps app_limited busy:199ms rcv_rtt:2438.63 rcv_space:14600 minrtt:11.178</span><br><span class="line">ESTAB 0 84288 172.16.210.17:3306 10.100.7.26:51160</span><br><span class="line"> cubic wscale:7,7 rto:216 rtt:15.129/0.314 ato:40 mss:1448 rcvmss:976 advmss:1448 cwnd:157 :157 bytes_acked:2954689465 bytes_received:1393 segs_out:2041403 segs_in:237797 data_segs_out:2041402 data_segs_in:8 send 120.2Mbps lastsnd:11 lastrcv:1103462 lastack:10 pacing_rate 144.2Mbps delivery_rate 31.3Mbps busy:1103503ms sndbuf_limited:3398ms(0.3%) unacked:24 retrans:0/7rcv_space:14600 notsent:49536 minrtt:9.551</span><br></pre></td></tr></table></figure>
<p>推荐 -m -i 一起查看状态,比如 rcv_space 表示buffer达到过的最大水位</p>
<blockquote>
<p><strong>rcv_space</strong> is the high water mark of the rate of the local application reading from the receive buffer during any RTT. This is used internally within the kernel to adjust sk_rcvbuf.</p>
</blockquote>
<h2 id="ss-查看拥塞窗口、RTO"><a href="#ss-查看拥塞窗口、RTO" class="headerlink" title="ss 查看拥塞窗口、RTO"></a>ss 查看拥塞窗口、RTO</h2><blockquote>
<p>//rto的定义,不让修改,每个ip的rt都不一样,必须通过rtt计算所得, HZ 一般是1秒<br>#define TCP_RTO_MAX ((unsigned)(120*HZ))<br>#define TCP_RTO_MIN ((unsigned)(HZ/5)) //在rt很小的环境中计算下来RTO基本等于TCP_RTO_MIN</p>
</blockquote>
<p>下面看到的rto和rtt单位都是毫秒,一般rto最小为200ms、最大为120秒</p>
<figure class="highlight plaintext"><table><tr><td class="gutter"><pre><span class="line">1</span><br><span class="line">2</span><br><span class="line">3</span><br><span class="line">4</span><br><span class="line">5</span><br><span class="line">6</span><br><span class="line">7</span><br><span class="line">8</span><br><span class="line">9</span><br></pre></td><td class="code"><pre><span class="line">#ss -itn |egrep "cwnd|rto" </span><br><span class="line">ESTAB 0 165 [::ffff:192.168.0.174]:48074 [::ffff:192.168.0.173]:3306</span><br><span class="line"> cubic wscale:7,7 rto:201 rtt:0.24/0.112 ato:40 mss:1448 rcvmss:1448 advmss:1448 cwnd:10 bytes_acked:1910206449 bytes_received:8847784416 segs_out:11273005 segs_in:22997562 data_segs_out:9818729 data_segs_in:13341573 send 482.7Mbps lastsnd:1 lastrcv:1 pacing_rate 963.8Mbps delivery_rate 163.2Mbps app_limited busy:2676463ms retrans:0/183 rcv_rtt:1.001 rcv_space:35904 minrtt:0.135</span><br><span class="line"></span><br><span class="line">ESTAB 0 0 [::ffff:192.168.0.174]:48082 [::ffff:192.168.0.173]:3306</span><br><span class="line"> cubic wscale:7,7 rto:201 rtt:0.262/0.112 ato:40 mss:1448 rcvmss:1448 advmss:1448 cwnd:10 bytes_acked:1852907381 bytes_received:8346503207 segs_out:10913962 segs_in:22169704 data_segs_out:9531411 data_segs_in:12796151 send 442.1Mbps lastsnd:2 lastack:2 pacing_rate 881.3Mbps delivery_rate 164.3Mbps app_limited busy:2736500ms retrans:0/260 rcv_rtt:1.042 rcv_space:31874 minrtt:0.133</span><br><span class="line"> </span><br><span class="line"> -----</span><br><span class="line"> skmem:(r0,rb131072,t0,tb133632,f0,w0,o0,bl0,d0) cubic wscale:8,7 rto:233 rtt:32.489/2.99 ato:40 mss:1380 rcvmss:536 advmss:1460 cwnd:11 ssthresh:8 bytes_acked:99862366 bytes_received:2943 segs_out:78933 segs_in:23388 data_segs_out:78925 data_segs_in:81 send 3.7Mbps lastsnd:1735288 lastrcv:1735252 lastack:1735252 pacing_rate 4.5Mbps delivery_rate 2.9Mbps busy:370994ms retrans:0/6479 reordering:5 rcv_space:14600 minrtt:27.984</span><br></pre></td></tr></table></figure>
<h3 id="RTO计算算法"><a href="#RTO计算算法" class="headerlink" title="RTO计算算法"></a>RTO计算算法</h3><p>RTO的计算依赖于RTT值,或者说一系列RTT值。rto=f(rtt)</p>
<figure class="highlight plaintext"><table><tr><td class="gutter"><pre><span class="line">1</span><br><span class="line">2</span><br><span class="line">3</span><br><span class="line">4</span><br><span class="line">5</span><br><span class="line">6</span><br><span class="line">7</span><br><span class="line">8</span><br><span class="line">9</span><br><span class="line">10</span><br><span class="line">11</span><br><span class="line">12</span><br><span class="line">13</span><br><span class="line">14</span><br><span class="line">15</span><br><span class="line">16</span><br><span class="line">17</span><br><span class="line">18</span><br></pre></td><td class="code"><pre><span class="line">1.1. 在没有任何rtt sample的时候,RTO <- TCP_TIMEOUT_INIT (1s)</span><br><span class="line"> 多次重传时同样适用指数回避算法(backoff)增加RTO </span><br><span class="line"></span><br><span class="line">1.2. 获得第一个RTT sample后,</span><br><span class="line"> SRTT <- RTT</span><br><span class="line"> RTTVAR <- RTT/2</span><br><span class="line"> RTO <- SRTT + max(G, K * RTTVAR)</span><br><span class="line">其中K=4, G表示timestamp的粒度(在CONFIG_HZ=1000时,粒度为1ms)</span><br><span class="line"></span><br><span class="line">1.3. 后续获得更多RTT sample后,</span><br><span class="line"> RTTVAR <- (1 - beta) * RTTVAR + beta * |SRTT - R|</span><br><span class="line"> SRTT <- (1 - alpha) * SRTT + alpha * R</span><br><span class="line">其中beta = 1/4, alpha = 1/8</span><br><span class="line"></span><br><span class="line">1.4. Whenever RTO is computed, if it is less than 1 second, then the</span><br><span class="line"> RTO SHOULD be rounder up to 1 second.</span><br><span class="line"></span><br><span class="line">1.5. A maximum value MAY be placed on RTO provided it is at least 60 seconds.</span><br></pre></td></tr></table></figure>
<p>RTTVAR表示的是平滑过的平均偏差,SRTT表示的平滑过的RTT。这两个值的具体含义会在后面介绍<br>具体实现的时候进一步的解释。<br>以上是计算一个初始RTO值的过程,当连续出现RTO超时后,<br>RTO值会用一个叫做指数回避的策略进行调整,下面来具体介绍。</p>
<h2 id="从系统cache中查看-tcp-metrics-item"><a href="#从系统cache中查看-tcp-metrics-item" class="headerlink" title="从系统cache中查看 tcp_metrics item"></a>从系统cache中查看 tcp_metrics item</h2><pre><code>$sudo ip tcp_metrics show | grep 100.118.58.7
100.118.58.7 age 1457674.290sec tw_ts 3195267888/5752641sec ago rtt 1000us rttvar 1000us ssthresh 361 cwnd 40 ----这两个值对传输性能很重要
192.168.1.100 age 1051050.859sec ssthresh 4 cwnd 2 rtt 4805us rttvar 4805us source 192.168.0.174 ---这条记录有问题,缓存的ssthresh 4 cwnd 2都太小,传输速度一定慢
清除 tcp_metrics, sudo ip tcp_metrics flush all
关闭 tcp_metrics 功能,net.ipv4.tcp_no_metrics_save = 1
sudo ip tcp_metrics delete 100.118.58.7
</code></pre>
<p>每个连接的ssthresh默认是个无穷大的值,但是内核会cache对端ip上次的ssthresh(大部分时候两个ip之间的拥塞窗口大小不会变),这样大概率到达ssthresh之后就基本拥塞了,然后进入cwnd的慢增长阶段。</p>
<h2 id="ss-过滤地址和端口号,类似tcpdump的用法"><a href="#ss-过滤地址和端口号,类似tcpdump的用法" class="headerlink" title="ss 过滤地址和端口号,类似tcpdump的用法"></a>ss 过滤地址和端口号,类似tcpdump的用法</h2><p>过滤目标端口是80的或者源端口是1723的连接,dst后面要跟空格然后加“:”:</p>
<pre><code># ss -ant dst :80 or src :1723
State Recv-Q Send-Q Local Address:Port Peer Address:Port
LISTEN 0 3 *:1723 *:*
TIME-WAIT 0 0 172.31.23.95:37269 111.161.68.235:80
TIME-WAIT 0 0 172.31.23.95:37263 111.161.68.235:80
TIME-WAIT 0 0 172.31.23.95:37267
</code></pre>
<p>or:</p>
<pre><code>ss -ant dport = :80 or sport = :1723
</code></pre>
<p>地址筛选,目标地址是111.161.68.235的连接</p>
<pre><code>ss -ant dst 111.161.68.235
</code></pre>
<p>端口大小筛选,源端口大于1024的端口:</p>
<pre><code>ss sport gt 1024
</code></pre>
<p>How Do I Compare Local and/or Remote Port To A Number?<br>Use the following syntax:</p>
<pre><code>## Compares remote port to a number ##
ss dport OP PORT
## Compares local port to a number ##
sport OP PORT
</code></pre>
<p>Where OP can be one of the following:</p>
<pre><code><= or le : Less than or equal to port
>= or ge : Greater than or equal to port
== or eq : Equal to port
!= or ne : Not equal to port
< or gt : Less than to port
> or lt : Greater than to port
Note: le, gt, eq, ne etc. are use in unix shell and are accepted as well.
###################################################################################
### Do not forget to escape special characters when typing them in command line ###
###################################################################################
ss sport = :http
ss dport = :http
ss dport \> :1024
ss sport \> :1024
ss sport \< :32000
ss sport eq :22
ss dport != :22
ss state connected sport = :http
ss \( sport = :http or sport = :https \)
ss -o state fin-wait-1 \( sport = :http or sport = :https \) dst 192.168.1/24
</code></pre>
<h2 id="ss-查看-timer-状态"><a href="#ss-查看-timer-状态" class="headerlink" title="ss 查看 timer 状态"></a>ss 查看 timer 状态</h2><p>ss -atonp</p>
<h2 id="按连接状态过滤"><a href="#按连接状态过滤" class="headerlink" title="按连接状态过滤"></a>按连接状态过滤</h2><p>Display All Established HTTP Connections</p>
<pre><code>ss -o state established '( dport = :http or sport = :http )'
</code></pre>
<p>List all the TCP sockets in state -FIN-WAIT-1 for our httpd to network 202.54.1/24 and look at their timers:<br> ss -o state fin-wait-1 ‘( sport = :http or sport = :https )’ dst 202.54.1/24</p>
<p>Filter Sockets Using TCP States</p>
<pre><code>ss -4 state FILTER-NAME-HERE
</code></pre>
<p>Where FILTER-NAME-HERE can be any one of the following,</p>
<pre><code>established
syn-sent
syn-recv
fin-wait-1
fin-wait-2
time-wait
closed
close-wait
last-ack
listen
closing
all : All of the above states
connected : All the states except for listen and closed
synchronized : All the connected states except for syn-sent
bucket : Show states, which are maintained as minisockets, i.e. time-wait and syn-recv.
big : Opposite to bucket state.
</code></pre>
<h2 id="ss分析重传的包数量"><a href="#ss分析重传的包数量" class="headerlink" title="ss分析重传的包数量"></a>ss分析重传的包数量</h2><p>通过抓取ss命令,可以分析出来重传的包数量,然后将重传的流的数量和重传的包的数量按照对端IP:port的维度分段聚合,参考命令:</p>
<pre><code>ss -itn |grep -v "Address:Port" | xargs -L 1 | grep retrans | awk '{gsub("retrans:.*/", "",$21); print $5, $21}' | awk '{arr[$1]+=$2} END {for (i in arr) {print i,arr[i]}}' | sort -rnk 2
</code></pre>
<p>xargs <strong>-L 1</strong> 每一行处理一次,但是这个行如果是空格、tab结尾,那么会被认为是连续行,跟下一行合并</p>
<p>高版本Linux内核的话,可以用systemtap或者bcc来获取每个连接的重传包以及发生重传的阶段</p>
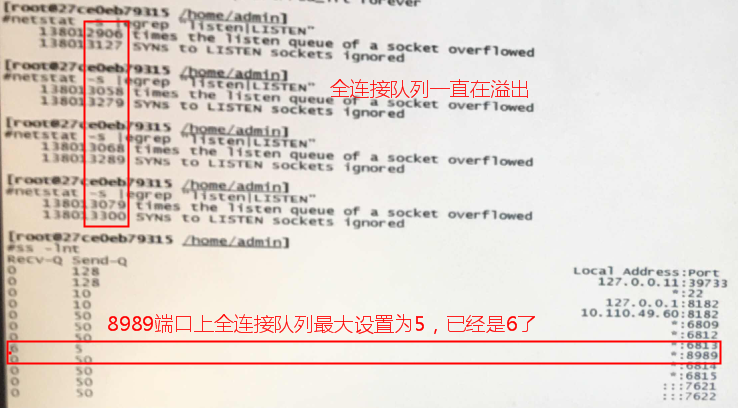
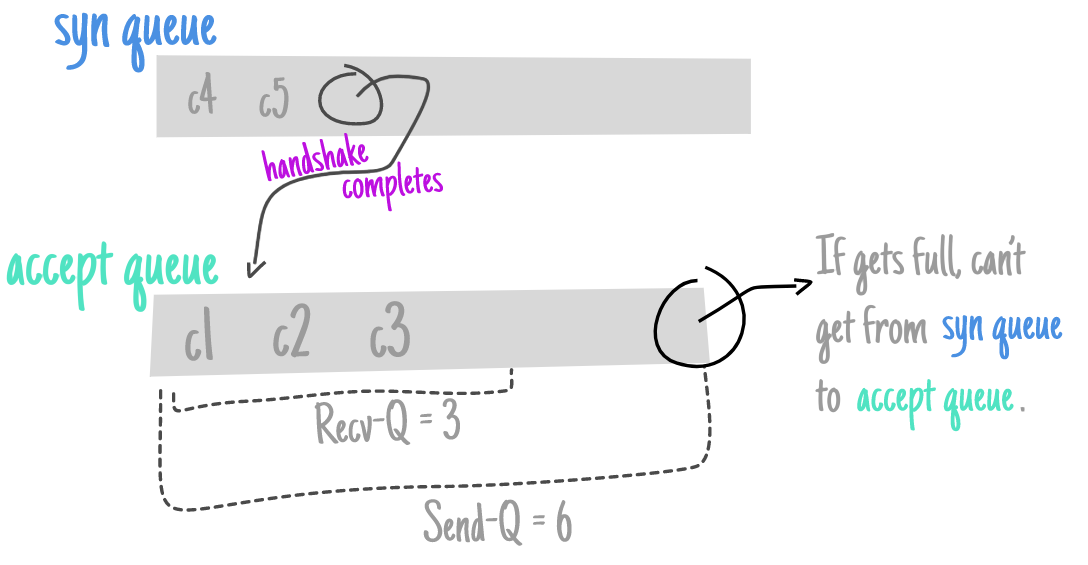
<h2 id="当前和最大全连接队列确认"><a href="#当前和最大全连接队列确认" class="headerlink" title="当前和最大全连接队列确认"></a>当前和最大全连接队列确认</h2><pre><code>$ss -lt
State Recv-Q Send-Q Local Address:Port Peer Address:Port
LISTEN 0 128 127.0.0.1:10248 *:*
LISTEN 0 128 *:2376 *:*
LISTEN 0 128 127.0.0.1:10249 *:*
LISTEN 0 128 *:7337 *:*
LISTEN 0 128 *:10250 *:*
LISTEN 0 128 11.163.187.44:7946 *:*
LISTEN 0 128 127.0.0.1:55631 *:*
LISTEN 0 128 *:10256 *:*
LISTEN 0 10 *:6640 *:*
LISTEN 0 128 127.0.0.1:vmware-fdm *:*
LISTEN 0 128 11.163.187.44:vmware-fdm *:*
LISTEN 0 128 *:ssh *:*
LISTEN 0 10 127.0.0.1:15772 *:*
LISTEN 0 10 127.0.0.1:15776 *:*
LISTEN 0 10 127.0.0.1:19777 *:*
LISTEN 0 10 11.163.187.44:15778 *:*
LISTEN 0 128 *:tr-rsrb-p2 *:*
</code></pre>
<h2 id="ss-s"><a href="#ss-s" class="headerlink" title="ss -s"></a>ss -s</h2><p>统计所有连接的状态</p>
<h2 id="nstat"><a href="#nstat" class="headerlink" title="nstat"></a>nstat</h2><p>nstat -z -t 1 类似 netstat -s (ss –info 展示rto、拥塞算法等更详细信息; netstat -ant -o 展示keepalive是否)</p>
<p>netstat<a target="_blank" rel="noopener" href="http://perthcharles.github.io/2015/11/10/wiki-netstat-proc/">参考</a></p>
<p>比如:</p>
<figure class="highlight plaintext"><table><tr><td class="gutter"><pre><span class="line">1</span><br><span class="line">2</span><br><span class="line">3</span><br><span class="line">4</span><br><span class="line">5</span><br></pre></td><td class="code"><pre><span class="line">#nstat -az TcpExtTCPRcvCollapsed TcpExtTCPRcvCoalesce TcpExtTCPRcvQDrop</span><br><span class="line">#kernel</span><br><span class="line">TcpExtTCPRcvCollapsed 0 0.0 //类似对内存进行垃圾回收,慢</span><br><span class="line">TcpExtTCPRcvCoalesce 403679 0.0 //合并整理,较快</span><br><span class="line">TcpExtTCPRcvQDrop 0 0.0</span><br></pre></td></tr></table></figure>
<p>参考 <a target="_blank" rel="noopener" href="https://blog.cloudflare.com/when-the-window-is-not-fully-open-your-tcp-stack-is-doing-more-than-you-think">cloudflare 博客</a>:</p>
<p><img src="/images/951413iMgBlog/image5-13.png" alt="img"></p>
<p><img src="/images/951413iMgBlog/image8-4.png" alt="img"></p>
<h2 id="knetstat"><a href="#knetstat" class="headerlink" title="knetstat"></a>knetstat</h2><p>最后给出的一个工具,knetstat(需要单独安装),也可以查看tcp的状态下的各种参数,需要单独安装</p>
<p>example(3306是本地server,4192是后端MySQL):</p>
<pre><code>Recv-Q Send-Q Local Address Foreign Address Stat Diag Options
0 0 0.0.0.0:3306 0.0.0.0:* LSTN SO_REUSEADDR=1,SO_REUSEPORT=0,SO_KEEPALIVE=0,TCP_NODELAY=0,TCP_FASTOPEN=0,TCP_DEFER_ACCEPT=0
0 0 0.0.0.0:3406 0.0.0.0:* LSTN SO_REUSEADDR=1,SO_REUSEPORT=0,SO_KEEPALIVE=0,TCP_NODELAY=0,TCP_FASTOPEN=0,TCP_DEFER_ACCEPT=0
0 0 127.0.0.1:8182 0.0.0.0:* LSTN SO_REUSEADDR=1,SO_REUSEPORT=0,SO_KEEPALIVE=0,TCP_NODELAY=0,TCP_FASTOPEN=0,TCP_DEFER_ACCEPT=0
0 0 10.0.186.73:8182 0.0.0.0:* LSTN SO_REUSEADDR=1,SO_REUSEPORT=0,SO_KEEPALIVE=0,TCP_NODELAY=0,TCP_FASTOPEN=0,TCP_DEFER_ACCEPT=0
0 0 0.0.0.0:22 0.0.0.0:* LSTN SO_REUSEADDR=1,SO_REUSEPORT=0,SO_KEEPALIVE=0,TCP_NODELAY=0,TCP_FASTOPEN=0,TCP_DEFER_ACCEPT=0
0 0 0.0.0.0:8188 0.0.0.0:* LSTN SO_REUSEADDR=1,SO_REUSEPORT=0,SO_KEEPALIVE=0,TCP_NODELAY=0,TCP_FASTOPEN=0,TCP_DEFER_ACCEPT=0
0 0 127.0.0.1:15778 0.0.0.0:* LSTN SO_REUSEADDR=1,SO_REUSEPORT=0,SO_KEEPALIVE=0,TCP_NODELAY=0,TCP_FASTOPEN=0,TCP_DEFER_ACCEPT=0
0 138 10.0.186.73:51756 10.0.160.1:4192 ESTB ># SO_REUSEADDR=0,SO_REUSEPORT=0,SO_KEEPALIVE=1,TCP_NODELAY=1,TCP_DEFER_ACCEPT=0
0 0 10.0.186.73:3306 10.0.186.70:37428 ESTB SO_REUSEADDR=1,SO_REUSEPORT=0,SO_KEEPALIVE=1,SO_RCVBUF=32768,SO_SNDBUF=65536,TCP_NODELAY=1,TCP_DEFER_ACCEPT=0
0 138 10.0.186.73:51476 10.0.160.1:4192 ESTB ># SO_REUSEADDR=0,SO_REUSEPORT=0,SO_KEEPALIVE=1,TCP_NODELAY=1,TCP_DEFER_ACCEPT=0
0 0 10.0.186.73:3306 10.0.186.70:37304 ESTB SO_REUSEADDR=1,SO_REUSEPORT=0,SO_KEEPALIVE=1,SO_RCVBUF=32768,SO_SNDBUF=65536,TCP_NODELAY=1,TCP_DEFER_ACCEPT=0
0 0 10.0.186.73:51842 10.0.160.1:4192 ESTB SO_REUSEADDR=0,SO_REUSEPORT=0,SO_KEEPALIVE=1,TCP_NODELAY=1,TCP_DEFER_ACCEPT=0
44 0 10.0.186.73:3306 10.0.186.70:36238 ESTB SO_REUSEADDR=1,SO_REUSEPORT=0,SO_KEEPALIVE=1,SO_RCVBUF=32768,SO_SNDBUF=65536,TCP_NODELAY=1,TCP_DEFER_ACCEPT=0
44 0 10.0.186.73:3306 10.0.186.70:36160 ESTB SO_REUSEADDR=1,SO_REUSEPORT=0,SO_KEEPALIVE=1,SO_RCVBUF=32768,SO_SNDBUF=65536,TCP_NODELAY=1,TCP_DEFER_ACCEPT=0
0 0 10.0.186.73:19030 10.0.171.188:8000 TIMW
</code></pre>
<p>3306对应的client上:</p>
<pre><code>Recv-Q Send-Q Local Address Foreign Address Stat Diag Options
0 44 10.0.186.70:42428 10.0.186.73:3306 ESTB ># SO_REUSEADDR=0,SO_REUSEPORT=0,SO_KEEPALIVE=1,SO_RCVTIMEO=31536000000ms,SO_SNDTIMEO=31536000000ms,TCP_NODELAY=1,TCP_DEFER_ACCEPT=0
0 44 10.0.186.70:42298 10.0.186.73:3306 ESTB ># SO_REUSEADDR=0,SO_REUSEPORT=0,SO_KEEPALIVE=1,SO_RCVTIMEO=31536000000ms,SO_SNDTIMEO=31536000000ms,TCP_NODELAY=1,TCP_DEFER_ACCEPT=0
0 44 10.0.186.70:42296 10.0.186.73:3306 ESTB ># SO_REUSEADDR=0,SO_REUSEPORT=0,SO_KEEPALIVE=1,SO_RCVTIMEO=31536000000ms,SO_SNDTIMEO=31536000000ms,TCP_NODELAY=1,TCP_DEFER_ACCEPT=0
0 44 10.0.186.70:42322 10.0.186.73:3306 ESTB ># SO_REUSEADDR=0,SO_REUSEPORT=0,SO_KEEPALIVE=1,SO_RCVTIMEO=31536000000ms,SO_SNDTIMEO=31536000000ms,TCP_NODELAY=1,TCP_DEFER_ACCEPT=0
</code></pre>
<p>Diag列的说明 <br> Indicator Meaning<br> >| The sender window (i.e. the window advertised by the remote endpoint) is 0. No data can be sent to the peer.<br> >|< The receiver window (i.e. the window advertised by the local endpoint) is 0. No data can be received from the peer.<br> ><br> ># There are unacknowledged packets and the last ACK was received more than one second ago. This may be an indication that there are network problems or that the peer crashed.</p>
<h2 id="参考文章"><a href="#参考文章" class="headerlink" title="参考文章"></a>参考文章</h2><p><a target="_blank" rel="noopener" href="https://www.cyberciti.biz/tips/linux-investigate-sockets-network-connections.html">https://www.cyberciti.biz/tips/linux-investigate-sockets-network-connections.html</a></p>
<p><a target="_blank" rel="noopener" href="http://perthcharles.github.io/2015/11/10/wiki-netstat-proc/">http://perthcharles.github.io/2015/11/10/wiki-netstat-proc/</a></p>
<p>源代码:<a target="_blank" rel="noopener" href="https://github.com/sivasankariit/iproute2/blob/master/misc/ss.c">https://github.com/sivasankariit/iproute2/blob/master/misc/ss.c</a></p>
<p><a target="_blank" rel="noopener" href="https://github.com/veithen/knetstat/tree/master">https://github.com/veithen/knetstat/tree/master</a></p>
<p><a target="_blank" rel="noopener" href="https://access.redhat.com/discussions/782343">https://access.redhat.com/discussions/782343</a></p>
<p><a target="_blank" rel="noopener" href="https://perthcharles.github.io/2015/09/06/wiki-rtt-estimator/">RTO的计算方法(基于RFC6298和Linux 3.10)</a></p>
</div>
<footer class="post-footer">
<div class="post-eof"></div>
</footer>
</article>
</div>
<nav class="pagination">
<a class="extend prev" rel="prev" title="上一页" aria-label="上一页" href="/page/19/"><i class="fa fa-angle-left"></i></a><a class="page-number" href="/">1</a><span class="space">…</span><a class="page-number" href="/page/19/">19</a><span class="page-number current">20</span><a class="page-number" href="/page/21/">21</a><a class="extend next" rel="next" title="下一页" aria-label="下一页" href="/page/21/"><i class="fa fa-angle-right"></i></a>
</nav>
</div>
</main>
<footer class="footer">
<div class="footer-inner">
<div class="copyright">
©
<span itemprop="copyrightYear">2026</span>
<span class="with-love">
<i class="fa fa-heart"></i>
</span>
<span class="author" itemprop="copyrightHolder">twitter @plantegg</span>
</div>
<div class="busuanzi-count">
<span class="post-meta-item" id="busuanzi_container_site_uv">
<span class="post-meta-item-icon">
<i class="fa fa-user"></i>
</span>
<span class="site-uv" title="总访客量">
<span id="busuanzi_value_site_uv"></span>
</span>
</span>
<span class="post-meta-item" id="busuanzi_container_site_pv">
<span class="post-meta-item-icon">
<i class="fa fa-eye"></i>
</span>
<span class="site-pv" title="总访问量">
<span id="busuanzi_value_site_pv"></span>
</span>
</span>
</div>
<div class="powered-by">由 <a href="https://hexo.io/" rel="noopener" target="_blank">Hexo</a> & <a href="https://theme-next.js.org/muse/" rel="noopener" target="_blank">NexT.Muse</a> 强力驱动
</div>
</div>
</footer>
<div class="toggle sidebar-toggle" role="button">
<span class="toggle-line"></span>
<span class="toggle-line"></span>
<span class="toggle-line"></span>
</div>
<div class="sidebar-dimmer"></div>
<div class="back-to-top" role="button" aria-label="返回顶部">
<i class="fa fa-arrow-up fa-lg"></i>
<span>0%</span>
</div>
<noscript>
<div class="noscript-warning">Theme NexT works best with JavaScript enabled</div>
</noscript>
</body>
</html>